Karolium vs Threat Watch
Side-by-side comparison to help you choose the right tool.
Build intelligent apps 10X faster with Karolium's unified zero-code AI platform!.
Last updated: February 28, 2026
Threat Watch
Instantly scan your cybersecurity health and get actionable insights to protect yourself now!.
Last updated: March 1, 2026
Visual Comparison
Karolium

Threat Watch
Feature Comparison
Karolium
Unified Zero-Code Platform
Unleash incredible speed and flexibility with a single platform that merges integration, application, operations, and AI capabilities! This unified environment allows you to connect systems, build apps, manage operations, and infuse AI—all through a visual, code-free interface. Say goodbye to dependency on developers and hello to empowering your business teams to create and customize solutions at an unprecedented pace!
Pre-Composed Value Chain Modules
Hit the ground running with a suite of ready-to-use, enterprise-grade modules designed for the modern supply chain! Accelerate your digital projects with out-of-the-box solutions for Supplier Collaboration, Smart Warehousing, AI-Driven Demand Forecasting, Contract Manufacturing, and more. These modules are fully composable, allowing you to tailor them perfectly to your unique workflows without starting from scratch!
Built-In Enterprise Intelligence
Embed predictive and prescriptive analytics directly into your business applications! Karolium isn't just a builder; it's an intelligence platform. Leverage built-in AI for image recognition, lead time prediction, asset monitoring, and digital twin creation. Make proactive, data-driven decisions and create applications that don't just record data, but actively recommend the best course of action!
Unlimited Customization & Scalability
Experience boundless adaptability with an enterprise PaaS that supports unlimited users and endless customization! Modify pre-packaged modules or compose entirely new ones to fit your exact needs. The platform scales with you, delivering new capabilities and enhancements with every quarterly release, ensuring your solutions never become obsolete!
Threat Watch
Comprehensive Digital Risk Assessment
Go beyond basic scans and get a complete health check for your entire digital footprint! Threat Watch continuously evaluates critical security categories including compromised credentials, breached accounts, vulnerable devices, and phishing threats, giving you a unified score and clear understanding of where you stand. No more guessing about your security posture!
Dark Web & Deep Web Surveillance
Gain a crucial advantage by monitoring places where threats hide! Our platform actively scans the dark and deep web for your organization's stolen data, leaked credentials, and mentions of your assets. Discover breaches you didn't even know about and take action before attackers can exploit them!
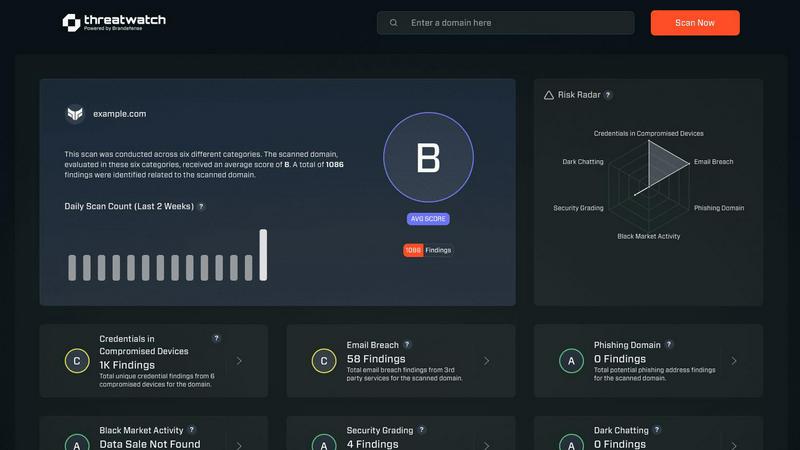
Real-Time Threat Intelligence Dashboard
See everything you need in one glance with our dynamic, intuitive command center! The dashboard provides a real-time, visual overview of your cyber health, alerting you to new risks as they emerge. Track trends, monitor key risk indicators, and make informed decisions without sifting through endless reports!
Automated Exposure Prioritization
Not all risks are created equal, and Threat Watch knows it! The platform doesn't just find problems; it intelligently analyzes and prioritizes them based on severity and potential business impact. Focus your team's efforts on what matters most and remediate critical vulnerabilities before they can be exploited!
Use Cases
Karolium
Augmenting Core ERP & Legacy Systems
Breathe new life into your existing software investments! Easily extend the functionality of your core ERP or legacy systems by building custom interfaces, workflows, and reports on top of them with zero code. Connect disparate systems seamlessly and create a unified, modern user experience without the risk and cost of a full system replacement!
Rapid Supply Chain Innovation
Revolutionize your supply chain operations at lightning speed! Deploy pre-composed modules for supplier collaboration and centralized procurement to enhance real-time coordination. Implement AI-infused demand forecasting and lead time prediction to move from reactive to proactive planning, all without complex point-to-point integrations!
Building AI-Driven Business Applications
Democratize AI and put its power directly in the hands of your business teams! Use the code-free environment to create intelligent applications for specific needs, such as automated quality checks via image recognition or predictive maintenance for critical assets. Turn AI ambition into tangible, operational reality quickly and efficiently!
Accelerating Custom Workflow Automation
Eliminate manual bottlenecks and paper-based processes across departments! Whether it's for HR onboarding, compliance tracking, or field service management, rapidly build tailored workflow applications that automate approvals, notifications, and data collection. Streamline operations and boost productivity without waiting for IT backlog!
Threat Watch
Proactive Security Posture Management
Move from a reactive security model to a proactive powerhouse! IT leaders and CISOs use Threat Watch to continuously monitor their organization's external security posture, identify weaknesses before they are attacked, and report to the board with data-backed confidence about their cyber resilience.
Rapid Incident Response & Breach Verification
When a data breach is suspected or reported, speed is everything! Security teams leverage Threat Watch to quickly verify if company credentials or data have actually been leaked online, understand the scope of the exposure, and immediately begin containment and notification processes.
Third-Party & Supply Chain Risk Assessment
Your security is only as strong as your weakest vendor link! Procurement and risk management teams use Threat Watch to evaluate the cybersecurity health of potential and existing partners. Discover if their breaches could impact your data and make smarter, safer business relationships.
Executive-Level Risk Reporting & Compliance
Simplify complex security data for business leadership! Executives and compliance officers use the clear, dashboard-driven insights from Threat Watch to understand business risk, demonstrate due diligence, and support compliance with frameworks that require monitoring for data leaks and exposures.
Overview
About Karolium
Welcome to the future of enterprise agility with Karolium! This revolutionary platform is your all-in-one solution for supercharged digital transformation! Designed for forward-thinking businesses, Karolium is a unified zero-code platform that combines the power of iPaaS, aPaaS, oPaaS, and AIPaaS into a single, dynamic environment. It empowers teams across any industry to rapidly build, customize, extend, and deploy powerful, intelligent applications without writing a single line of code! Imagine seamlessly augmenting your existing software ecosystem and constructing tailored business solutions at 10x traditional speed, all while breaking free from the limitations of rigid, off-the-shelf software and costly custom development cycles. Karolium's core value proposition is a powerful trifecta: it's a codeless application builder, an enterprise intelligence platform with built-in AI, and a suite of ready-to-deploy value chain modules. This means you can create apps that predict and prescribe optimal actions, accelerate critical projects like supplier collaboration or smart warehousing, and drive tangible business outcomes—all on one agile, subscription-based SaaS platform. Transform your complexity into clarity and your legacy systems into dynamic assets with Karolium!
About Threat Watch
Stop operating in the dark and start commanding your cybersecurity destiny! Threat Watch is your all-in-one cybersecurity intelligence command center, designed to deliver unparalleled, real-time visibility into your organization's complete digital risk landscape! This powerful, unified platform is the ultimate tool for IT leaders, security teams, and business executives who are tired of reactive panic and ready for proactive, data-driven control. It continuously scans and analyzes your assets, vulnerabilities, and critical exposures across the clear, deep, and dark web to deliver a crystal-clear picture of your cyber health instantly. By automating complex threat assessments and distilling overwhelming data into immediate, actionable insights, Threat Watch empowers you to uncover hidden threats, prioritize the most critical risks with confidence, and take decisive mitigation action faster than ever before. Transform uncertainty into absolute confidence and data into a powerful security strategy!
Frequently Asked Questions
Karolium FAQ
What makes Karolium different from other low-code/no-code platforms?
Karolium stands out as a unified enterprise-grade platform that combines application building with deep integration, operations management, and built-in AI capabilities—all in one! It goes beyond simple app creation by offering pre-composed value-chain solutions specifically for complex business environments, enabling 10x faster development and deployment for serious digital transformation!
Can Karolium integrate with our current software like SAP or Oracle?
Absolutely! Seamless integration is a core strength of Karolium's unified platform. It is designed to connect effortlessly with both legacy systems (like SAP, Oracle) and modern microservices-based applications. You can augment and extend your current ecosystem without disruptive replacements, creating a cohesive and agile technology landscape!
Is technical expertise required to use Karolium?
No! That's the power of a true zero-code platform. Karolium is built for business analysts, process experts, and teams in operations, supply chain, and other domains to build and customize applications visually. You design solutions using intuitive drag-and-drop tools and visual workflows, eliminating the need for traditional programming skills!
How does the platform handle updates and new features?
Karolium is delivered as a managed PaaS-driven SaaS platform, meaning you get continuous access to the latest innovations without hassle! We provide regular platform enhancements and release new pre-composed value chain modules every quarter. Your applications automatically benefit from the latest capabilities, ensuring you always have a future-ready solution!
Threat Watch FAQ
What does Threat Watch actually scan and monitor?
Threat Watch conducts a comprehensive scan of your digital footprint! It actively monitors the clear web, deep web, and dark web for critical threats specific to your organization. This includes searching for compromised employee credentials, breached company accounts, vulnerable devices connected to your network, phishing sites targeting your brand, and other exposed sensitive data.
How quickly can I see results after starting a scan?
Incredibly fast! The moment you initiate your scan, Threat Watch begins processing data and delivering insights. You will start seeing initial results and a clear overview of your cybersecurity health almost immediately, with continuous, real-time updates as the platform discovers new threats and information across the web.
Is Threat Watch suitable for a small business without a dedicated IT team?
Absolutely! Threat Watch is built to be powerful yet accessible. The intuitive dashboard and automated prioritization are designed to give clear, actionable insights to users of all technical levels. It empowers small business owners to understand their real risk without needing a large security team, turning complex data into simple action steps.
What kind of actions can I take based on Threat Watch's findings?
Threat Watch empowers decisive action! Upon discovering a threat, you can immediately launch remediation workflows. This includes forcing password resets for compromised accounts, patching or isolating vulnerable devices, taking down phishing sites, alerting affected employees, and strengthening security policies to prevent future exposures of the same type.
Alternatives
Karolium Alternatives
Karolium is a dynamic, unified zero-code platform designed to accelerate digital transformation! It falls squarely into the codeless development and enterprise AI application space, empowering businesses to build custom solutions at incredible speed. Users often explore alternatives for various reasons! This could be due to specific budget constraints, the need for different integration capabilities, or a desire for a platform that aligns more closely with their existing tech stack and unique operational workflows. When evaluating other options, focus on core capabilities! Look for robust visual development tools, strong AI and analytics features, and seamless connectivity with your current software ecosystem. The goal is to find a platform that delivers agility without compromising on power or security!
Threat Watch Alternatives
Threat Watch is a dynamic cybersecurity intelligence platform that falls into the business intelligence category. It's designed to give organizations a real-time, actionable view of their digital risk by scanning for exposures across the clear, deep, and dark web! This powerful tool helps teams move from reactive panic to proactive, data-driven control of their security posture. Users often explore alternatives for various practical reasons! These can include budget considerations, the need for specific integrations with their existing tech stack, or requirements for different feature sets like more advanced reporting or compliance modules. Every organization's security journey and resources are unique, prompting a search for the perfect fit. When evaluating other options, focus on what matters most for your team's success! Look for comprehensive threat intelligence, real-time monitoring capabilities, and clear, actionable insights. The goal is to find a solution that transforms overwhelming data into a straightforward, executable security strategy, empowering you to act with confidence and speed.
