iGPT vs Threat Watch
Side-by-side comparison to help you choose the right tool.
Unlock your email's potential with iGPT, delivering instant, context-aware answers for smarter AI agent interactions!.
Last updated: February 28, 2026
Threat Watch
Instantly scan your cybersecurity health and get actionable insights to protect yourself now!.
Last updated: March 1, 2026
Visual Comparison
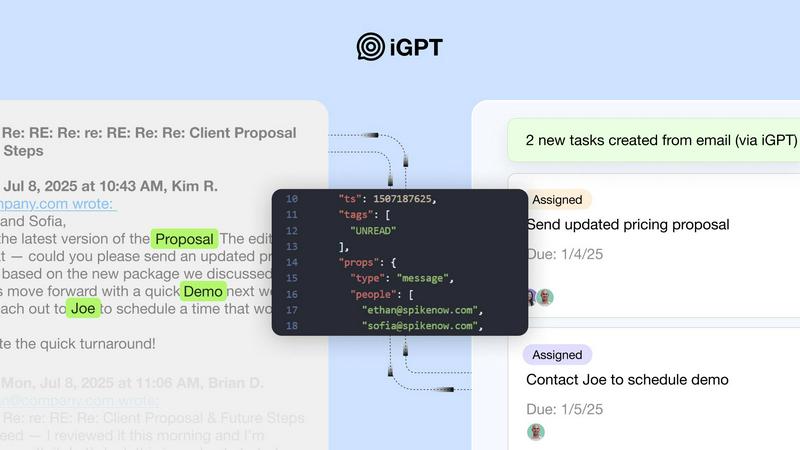
iGPT
Threat Watch
Feature Comparison
iGPT
Immediate Integration
iGPT offers a swift onboarding experience with its SDK and live playground, allowing you to test requests and responses in real-time. This immediate integration means you can hit the ground running without delays.
Unified Endpoint
Send a single request to the iGPT API that seamlessly runs retrieval, context shaping, and reasoning in one efficient pipeline. This unified endpoint simplifies your interactions with multiple data sources, making it easier to get the information you need.
Contextual Responses
Get ready for intelligent answers tailored to your specific queries! iGPT provides context-aware responses that are primed for reasoning and automation, complete with citations back to the original source messages and attachments.
Continuous Data Indexing
With iGPT, your data remains fresh and relevant! The API continuously indexes new messages and attachments, ensuring that your information is always up-to-date and readily accessible for your applications.
Threat Watch
Comprehensive Digital Risk Assessment
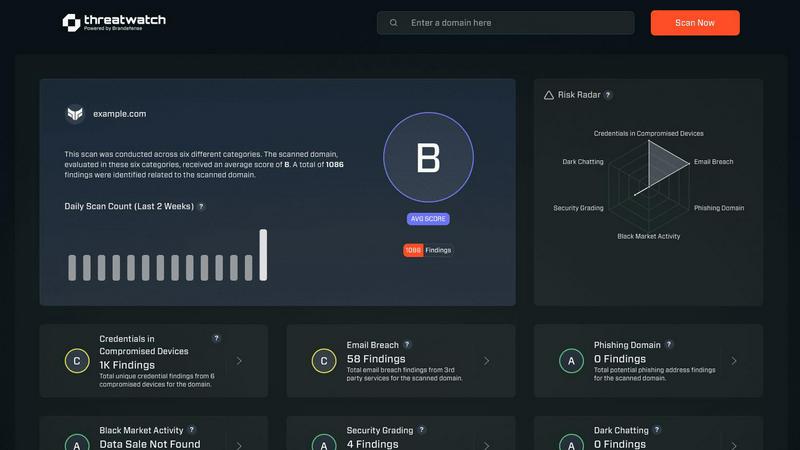
Go beyond basic scans and get a complete health check for your entire digital footprint! Threat Watch continuously evaluates critical security categories including compromised credentials, breached accounts, vulnerable devices, and phishing threats, giving you a unified score and clear understanding of where you stand. No more guessing about your security posture!
Dark Web & Deep Web Surveillance
Gain a crucial advantage by monitoring places where threats hide! Our platform actively scans the dark and deep web for your organization's stolen data, leaked credentials, and mentions of your assets. Discover breaches you didn't even know about and take action before attackers can exploit them!
Real-Time Threat Intelligence Dashboard
See everything you need in one glance with our dynamic, intuitive command center! The dashboard provides a real-time, visual overview of your cyber health, alerting you to new risks as they emerge. Track trends, monitor key risk indicators, and make informed decisions without sifting through endless reports!
Automated Exposure Prioritization
Not all risks are created equal, and Threat Watch knows it! The platform doesn't just find problems; it intelligently analyzes and prioritizes them based on severity and potential business impact. Focus your team's efforts on what matters most and remediate critical vulnerabilities before they can be exploited!
Use Cases
iGPT
Email Assistants
Transform your email management with iGPT-powered agents that can draft, prioritize, and take action on emails with full context. This capability significantly enhances productivity and reduces the time spent on email correspondence.
Workflow Automation
Leverage iGPT to convert email threads into actionable tasks, deadlines, and approvals. No more confusion about what's stuck in the pipeline—iGPT flags the roadblocks for you!
Support Copilots
Build support agents that can reconstruct the complete customer story through long email chains, attachments, and tone shifts. This ensures that customer interactions are smooth and well-informed, enhancing overall satisfaction.
CRM Agents
Extract essential decisions, owners, and deal momentum directly from email threads with iGPT. This functionality empowers your CRM systems with precise information that drives business outcomes and relationship management.
Threat Watch
Proactive Security Posture Management
Move from a reactive security model to a proactive powerhouse! IT leaders and CISOs use Threat Watch to continuously monitor their organization's external security posture, identify weaknesses before they are attacked, and report to the board with data-backed confidence about their cyber resilience.
Rapid Incident Response & Breach Verification
When a data breach is suspected or reported, speed is everything! Security teams leverage Threat Watch to quickly verify if company credentials or data have actually been leaked online, understand the scope of the exposure, and immediately begin containment and notification processes.
Third-Party & Supply Chain Risk Assessment
Your security is only as strong as your weakest vendor link! Procurement and risk management teams use Threat Watch to evaluate the cybersecurity health of potential and existing partners. Discover if their breaches could impact your data and make smarter, safer business relationships.
Executive-Level Risk Reporting & Compliance
Simplify complex security data for business leadership! Executives and compliance officers use the clear, dashboard-driven insights from Threat Watch to understand business risk, demonstrate due diligence, and support compliance with frameworks that require monitoring for data leaks and exposures.
Overview
About iGPT
Unlock the true potential of your communication data with iGPT! This enterprise-grade API revolutionizes how businesses interact with their email and messaging systems. iGPT transforms the unstructured chaos of emails, where critical decisions are made and projects are managed, into reliable, actionable intelligence. Tailored for developers and enterprises, iGPT allows you to create powerful applications that automate workflows without the hassle of data parsing, chunking, or prompt engineering. With just one API call, you can retrieve precise answers, extract structured data, and automate follow-ups, all while ensuring robust security and auditability. Say goodbye to wrestling with raw data and hello to the intelligent layer that your workflows truly deserve!
About Threat Watch
Stop operating in the dark and start commanding your cybersecurity destiny! Threat Watch is your all-in-one cybersecurity intelligence command center, designed to deliver unparalleled, real-time visibility into your organization's complete digital risk landscape! This powerful, unified platform is the ultimate tool for IT leaders, security teams, and business executives who are tired of reactive panic and ready for proactive, data-driven control. It continuously scans and analyzes your assets, vulnerabilities, and critical exposures across the clear, deep, and dark web to deliver a crystal-clear picture of your cyber health instantly. By automating complex threat assessments and distilling overwhelming data into immediate, actionable insights, Threat Watch empowers you to uncover hidden threats, prioritize the most critical risks with confidence, and take decisive mitigation action faster than ever before. Transform uncertainty into absolute confidence and data into a powerful security strategy!
Frequently Asked Questions
iGPT FAQ
How does iGPT ensure data security?
iGPT is designed with enterprise-grade protection at every layer. It employs role-based access control, zero data retention, and ensures your data is never used for training purposes.
Can iGPT handle attachments?
Absolutely! iGPT can extract text, data, and structure from various types of attachments, including documents, PDFs, and spreadsheets, making your email communications even more powerful.
Is there a playground to test iGPT?
Yes! iGPT provides a live playground where you can connect and test different data sources, allowing you to experience the API's capabilities in real-time before fully integrating it into your systems.
What types of businesses can benefit from iGPT?
iGPT is perfect for enterprises of all sizes that rely heavily on email communication. Whether you're in finance, customer support, or project management, iGPT can transform your email data into actionable insights!
Threat Watch FAQ
What does Threat Watch actually scan and monitor?
Threat Watch conducts a comprehensive scan of your digital footprint! It actively monitors the clear web, deep web, and dark web for critical threats specific to your organization. This includes searching for compromised employee credentials, breached company accounts, vulnerable devices connected to your network, phishing sites targeting your brand, and other exposed sensitive data.
How quickly can I see results after starting a scan?
Incredibly fast! The moment you initiate your scan, Threat Watch begins processing data and delivering insights. You will start seeing initial results and a clear overview of your cybersecurity health almost immediately, with continuous, real-time updates as the platform discovers new threats and information across the web.
Is Threat Watch suitable for a small business without a dedicated IT team?
Absolutely! Threat Watch is built to be powerful yet accessible. The intuitive dashboard and automated prioritization are designed to give clear, actionable insights to users of all technical levels. It empowers small business owners to understand their real risk without needing a large security team, turning complex data into simple action steps.
What kind of actions can I take based on Threat Watch's findings?
Threat Watch empowers decisive action! Upon discovering a threat, you can immediately launch remediation workflows. This includes forcing password resets for compromised accounts, patching or isolating vulnerable devices, taking down phishing sites, alerting affected employees, and strengthening security policies to prevent future exposures of the same type.
Alternatives
iGPT Alternatives
iGPT is an innovative API solution tailored for business intelligence, designed to empower AI agents with secure and instant access to the context embedded within email conversations and attachments. As organizations increasingly rely on email for critical business communications, users often seek alternatives to iGPT for various reasons, including pricing structures, specific feature requirements, or compatibility with their existing platforms. In the search for an alternative, it's essential to evaluate the capabilities of the API, the ease of integration, the level of support offered, and how well it addresses your organization's unique needs. When selecting an alternative, consider the functionality that best fits your workflow, including features such as context processing, data retrieval efficiency, and security measures. Look for solutions that provide a seamless user experience, simplify data handling, and enhance your overall productivity, ensuring that your communications remain actionable and insightful.
Threat Watch Alternatives
Threat Watch is a dynamic cybersecurity intelligence platform that falls into the business intelligence category. It's designed to give organizations a real-time, actionable view of their digital risk by scanning for exposures across the clear, deep, and dark web! This powerful tool helps teams move from reactive panic to proactive, data-driven control of their security posture. Users often explore alternatives for various practical reasons! These can include budget considerations, the need for specific integrations with their existing tech stack, or requirements for different feature sets like more advanced reporting or compliance modules. Every organization's security journey and resources are unique, prompting a search for the perfect fit. When evaluating other options, focus on what matters most for your team's success! Look for comprehensive threat intelligence, real-time monitoring capabilities, and clear, actionable insights. The goal is to find a solution that transforms overwhelming data into a straightforward, executable security strategy, empowering you to act with confidence and speed.
