B2B Email Verifier vs Cybersecurity Readiness Game
Side-by-side comparison to help you choose the right tool.
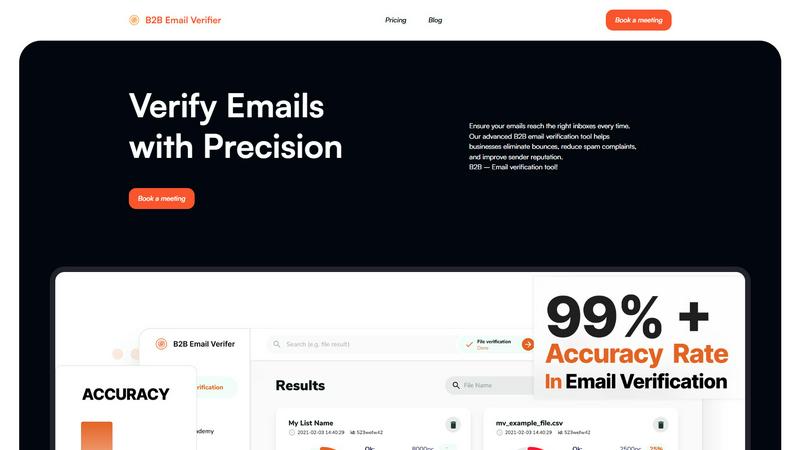
B2B Email Verifier
Boost your B2B outreach with 99% accurate email verification to eliminate bounces instantly!.
Last updated: February 28, 2026
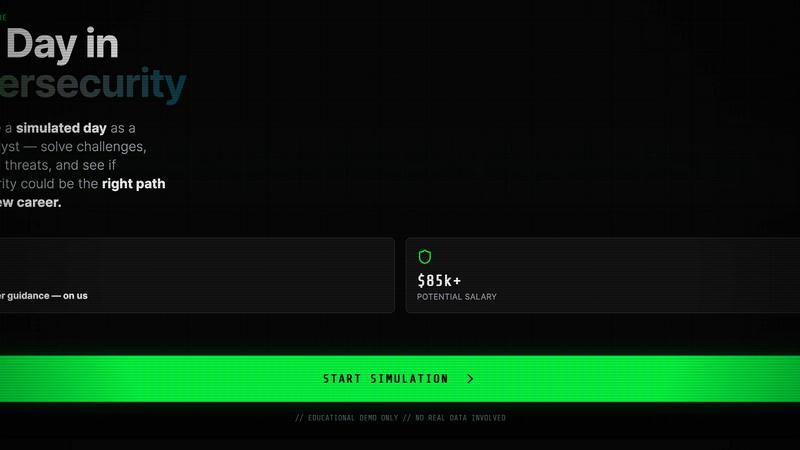
Cybersecurity Readiness Game
Test your team's cyber defense skills with a free, hands-on breach simulation game!.
Last updated: March 18, 2026
Visual Comparison
B2B Email Verifier
Cybersecurity Readiness Game
Feature Comparison
B2B Email Verifier
99%+ High Accuracy
Our advanced, proprietary algorithms are fine-tuned for the B2B landscape, ensuring over 99% accuracy in detecting valid, deliverable email addresses! We go beyond simple syntax checks to perform deep verification, catching typos, role-based addresses, and disposable emails that can harm your sender score. This unparalleled precision means you can launch every campaign with absolute confidence, knowing your messages will reach real people who can engage with your content and drive your business forward!
Bulk List Verification
Say goodbye to manual, time-consuming checks! Our bulk verification feature allows you to upload and cleanse entire lists of thousands of email addresses in mere seconds. Simply upload your CSV or TXT file, and our powerful system gets to work instantly, filtering out invalid, risky, and non-existent emails. This efficiency is a game-changer for preparing large-scale email marketing blasts, onboarding new lead lists, or maintaining the health of your existing CRM database without any tedious effort!
Real-Time API Verification
Integrate pristine email validation directly into your sign-up forms, lead capture pages, and CRM systems with our powerful Real-Time API! This feature acts as a gatekeeper, checking emails for validity at the very moment they are entered. It prevents invalid addresses from ever entering your system, saving you credits and protecting your sender reputation from the start. Ensure data quality flows seamlessly into your tech stack and automate your list hygiene for flawless, ongoing deliverability!
Secure & Encrypted Processing
Your data security is our top priority! We employ robust, end-to-end encryption throughout the entire verification process to ensure your valuable contact lists and customer information remain completely confidential and safe. You can trust that your sensitive B2B data is handled with the utmost care and never shared or misused. Focus on growing your business with peace of mind, knowing your assets are protected within our secure, reliable platform!
Cybersecurity Readiness Game
100% Free, No Registration Required
Jump into action immediately with zero barriers! We believe in accessible cybersecurity training for everyone. There's no sign-up form, no email capture, and no cost-just pure, unhindered learning. You can start a simulation session in seconds and focus entirely on building your skills without any administrative hassle. This feature ensures that individuals and teams can practice as often as they need, fostering a culture of continuous readiness!
Realistic, Scenario-Based Learning
Forget hypotheticals-you're in the hot seat! Our tool places you inside meticulously crafted, credible threat scenarios that mirror the challenges real security engineers face daily. From phishing campaigns to network intrusion attempts, each scenario unfolds based on your decisions, providing a safe but authentic environment to practice incident response. This hands-on approach transforms abstract concepts into tangible experience, making the learning stick far better than any textbook!
Clear Performance Metrics & Insights
Knowledge is power, especially when it's specific! After each simulation, you don't just get a pass/fail grade. You receive detailed performance insights that break down your decisions, evaluate their impact, and highlight key areas for improvement. These clear metrics allow you to track your progress over time, understand your decision-making patterns, and build a targeted plan to strengthen your cybersecurity readiness effectively!
Applied Decision-Making Practice
Build the critical thinking skills that define top cybersecurity pros! This feature is all about active engagement. You don't watch-you act. As the scenario progresses, you are prompted to make key decisions that determine the outcome. This constant practice in assessing risks, prioritizing actions, and mitigating threats under pressure is invaluable for developing the sharp instincts needed to protect real systems from actual attacks!
Use Cases
B2B Email Verifier
Supercharging Sales Outreach
Empower your sales development representatives (SDRs) to reach more genuine prospects faster! By verifying lead lists before launching cold email sequences, sales teams can eliminate bounces, avoid spam traps, and ensure their personalized pitches land in the right inboxes. This dramatically improves reply rates, increases meeting bookings, and accelerates the sales pipeline, turning your outreach efforts into a predictable revenue-generating machine!
Maximizing Marketing Campaign ROI
Transform your email marketing from a guessing game into a precision strategy! Marketing professionals can use B2B Email Verifier to cleanse their subscriber lists before every major campaign launch. This ensures newsletters, product announcements, and promotional offers are delivered to engaged, real users. The result? Sky-high open rates, improved click-through rates, and a significantly better return on investment for every marketing dollar spent!
Streamlining Recruitment Efforts
Recruiters and talent acquisition specialists can revolutionize their candidate outreach! Verify email addresses sourced from LinkedIn, resumes, or databases to ensure your job offers, interview invitations, and networking messages reach actual professionals. Stop wasting time on dead-end leads and focus your energy on connecting with qualified candidates who are ready to engage, making your recruitment process far more efficient and effective!
Maintaining CRM Health & Hygiene
Keep your customer relationship management (CRM) system clean and actionable! Regularly verify your entire contact database to identify and remove invalid email addresses that accumulate over time. This ongoing maintenance prevents communication breakdowns, ensures accurate analytics and reporting, and protects your company's sender reputation. A clean CRM is a powerful CRM, enabling every team to operate with reliable, high-quality data!
Cybersecurity Readiness Game
Career Exploration for Aspiring Professionals
Thinking about a career in cybersecurity? This game is your perfect first step! Get a genuine "one-day-in-the-life" taste of what a security engineer does without any commitment. The simulation helps you understand the role's demands, challenges, and required thought processes, allowing you to confidently decide if this exciting and high-demand field is the right path for you before investing in formal education!
Team Skill-Building & Internal Training
Transform your team from a potential vulnerability into your strongest defense! Managers can use this tool for regular, engaging internal training sessions. It's an excellent way to upskill existing IT staff, foster teamwork in incident response, and proactively address the human error factor that's involved in over 70% of breaches. It's cost-effective, scalable, and much more impactful than a standard security awareness video!
Readiness Assessment & Gap Identification
How prepared are you really? Move beyond checklist audits and get a practical, unbiased assessment of your or your team's cybersecurity readiness. The game acts as a diagnostic tool, revealing specific weak spots in processes and judgment. The performance insights provide a clear roadmap for where to focus your training efforts and resources to build a truly resilient security posture!
Interview Preparation & Skill Demonstration
Stand out in your next job interview! Candidates can use the simulation to hone their practical skills and even discuss their performance metrics and decision-making approach with potential employers. It's a powerful way to demonstrate proactive learning, hands-on problem-solving ability, and a genuine passion for cybersecurity, giving you a significant edge over other applicants!
Overview
About B2B Email Verifier
Stop letting email bounces and spam traps sabotage your outreach! B2B Email Verifier is your ultimate weapon for achieving pristine email deliverability and maximizing your campaign ROI. This powerful, advanced tool is engineered specifically for the unique challenges of business-to-business communication, ensuring your messages land in the right professional inboxes every single time! It's the perfect solution for sales teams, marketing professionals, recruiters, and any business that relies on cold email or newsletter campaigns to drive growth. By instantly identifying invalid, risky, or non-existent email addresses, our verifier empowers you to eliminate costly bounces, dramatically reduce spam complaints, and build an impeccable sender reputation. The core value proposition is crystal clear: transform your email list from a potential liability into your most reliable asset! With features like real-time verification and bulk list processing, you can enhance accuracy, boost engagement rates, and ensure your valuable content and offers actually reach your target audience. Get ready to captivate your customers and close more deals with confidence! Our platform is built on advanced algorithms that provide over 99% accuracy, giving you the confidence that your outreach efforts are built on a rock-solid foundation. It's more than just a tool; it's your strategic partner for scalable, successful business communication!
About Cybersecurity Readiness Game
Ready to test your cyber defense skills in a high-stakes, zero-risk environment? The Cybersecurity Readiness Game is your immersive, hands-on simulation tool that drops you directly into the heart of real-world threat scenarios! This isn't just another lecture or quiz-it's a dynamic, interactive experience where you make critical security decisions and see the immediate consequences of your actions. Designed for aspiring cybersecurity professionals, IT teams, and anyone curious about the field, this tool bridges the gap between theoretical knowledge and practical application. With no registration required, you can jump right in and start building the muscle memory needed for real incidents. The game provides clear, actionable performance insights, highlighting your strengths and pinpointing exactly where your skills need sharpening. It's the ultimate way to close the human error gap, build internal capability, and get a brutally honest, practical view of your true cybersecurity readiness. Stop wondering if you're prepared-find out for real!
Frequently Asked Questions
B2B Email Verifier FAQ
How does your email verifier work?
Our verifier uses a multi-step process to ensure maximum accuracy! When you submit an email, our system checks its syntax for correct formatting, verifies the domain and mail server exist and are configured to receive mail, and then performs a safe, non-intrusive ping to confirm the specific mailbox is active. This sophisticated combination of checks, powered by advanced algorithms, allows us to identify and filter out invalid, disposable, or risky addresses with over 99% precision!
Can I verify emails in bulk?
Absolutely, and it's incredibly fast! Our bulk verification feature is designed for efficiency. You can upload a list of thousands of email addresses via a CSV or TXT file. Our system processes the entire list in seconds, providing you with a detailed report that categorizes each address as valid, invalid, risky, or unknown. This allows you to quickly clean large lists for campaigns, migrate data, or audit your existing database with minimal effort!
Can I receive support if I need it?
Yes, we offer dedicated support to all our users! We believe in partnering with you for success. If you have any questions, encounter issues, or need guidance on best practices, our friendly and knowledgeable support team is ready to assist you. We are committed to providing the help you need to maximize your results with our B2B Email Verifier tool and ensure your outreach is always on target!
What happens if I exceed my credit limit?
If you use all the verification credits in your monthly plan, don't worry! You can easily purchase additional credit packs to continue verifying emails without interruption. Alternatively, you can upgrade to a higher plan that offers more credits to match your growing business needs. We provide flexible options to ensure your email verification processes never have to slow down, keeping your campaigns moving forward at full speed!
Cybersecurity Readiness Game FAQ
What is cybersecurity readiness?
Cybersecurity readiness is the proactive state of being prepared to prevent, detect, respond to, and recover from cyber threats and incidents. It's not just about having tools in place; it's about ensuring people and processes are trained and tested to use those tools effectively under pressure. Our game directly builds this readiness by simulating real incidents for practice!
Why is cybersecurity readiness important?
It's critically important for three key reasons! First, cybercrime is massively costly, projected to hit $10.5 trillion annually-strong readiness limits financial damage. Second, human error is involved in most breaches, so training people is essential. Third, there's a global shortage of over 3 million cybersecurity professionals, making it vital to build skills within your existing teams!
Is AI replacing cybersecurity jobs?
Absolutely not! While AI is a powerful tool for automating certain tasks like threat detection, it creates more need for human experts. Cybersecurity professionals are needed to manage AI systems, interpret complex results, make strategic decisions, and respond to sophisticated social engineering attacks that target human psychology. The field is growing, not shrinking!
What are the stages of cybersecurity?
While frameworks vary, a common structure includes five key stages: Identify, Protect, Detect, Respond, and Recover. Our Cybersecurity Readiness Game primarily focuses on the crucial "Respond" and "Recover" stages, giving you hands-on practice in containing threats, eradicating attackers, and restoring systems-a skillset that is essential in any comprehensive security strategy!
Alternatives
B2B Email Verifier Alternatives
B2B Email Verifier is a top-tier productivity tool designed to supercharge your professional outreach by ensuring near-perfect email deliverability! It instantly verifies and cleans your contact lists, eliminating bounces and protecting your sender reputation with incredible accuracy. Businesses often explore alternatives for various strategic reasons! You might be looking for a different pricing model, need specific integrations with your existing CRM or marketing stack, or require a unique feature set that better matches your team's workflow. It's all about finding the perfect fit for your unique growth engine! When evaluating other options, focus on core capabilities like verification accuracy, processing speed for bulk lists, and robust data security. A great alternative should empower your campaigns, seamlessly fit into your process, and deliver undeniable value to help you reach more inboxes and close more deals!
Cybersecurity Readiness Game Alternatives
The Cybersecurity Readiness Game is a dynamic productivity and management tool that transforms your team's learning! It immerses participants in real-world breach simulations to practice critical decisions, building essential skills and closing the human error gap with no registration required. Users often explore alternatives for various reasons, such as budget constraints, the need for different feature sets like advanced reporting or specific scenario libraries, or compatibility with other training platforms. Finding the right fit is key to an effective cybersecurity training program. When evaluating other options, prioritize tools that offer credible, hands-on scenarios, provide clear performance insights, and genuinely improve your team's practical readiness. Look for solutions that are engaging and directly address the human factors in your security posture!
